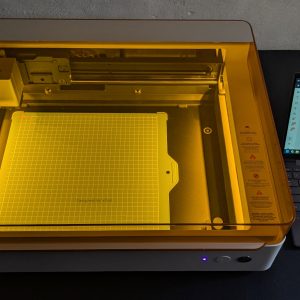
In the last part of this short series, we looked at the setup and commissioning. We also used an example project to illustrate the functionality of the first available module – the pen holder. Today we continue with exactly that, but with a different attachment and module. If you missed the first part, you can catch up on it here: Initial [...]
LeakWatch 2025 – Analysis of security incidents, data leaks and zero-day exploits in calendar week 49